Stile nordico Zanzariera Fatti A Mano Quattro colore Tenda Chiffon Tenda Letto A Baldacchino Castello Casetta Per Bambini Del Bambino Camera Da Letto|Zanzariere per culle| - AliExpress

Maniglia dello schermo del cavo della zanzariera della tenuta della mano sulla finestra della casa | Foto Premium

31 Linea 90x220CM Onda Fatto a mano Zanzariera Perline in legno Tenda Tenda Porta in legno Tenda Tenda per Portico Camera da letto Soggiorno Divisorio acquista in modo economico — spedizione gratuita,

Schiaccia Stop zanzariera magnetica: dove si acquista e come funziona? Opinioni e recensioni, prezzo – Pensieri fatti a mano

Zanzariera fatta a mano tenda di perline di legno 220x90cm 31 linee tende per porte in legno tende cucina di casa camera da letto bagno portico divisore|Tende| - AliExpress

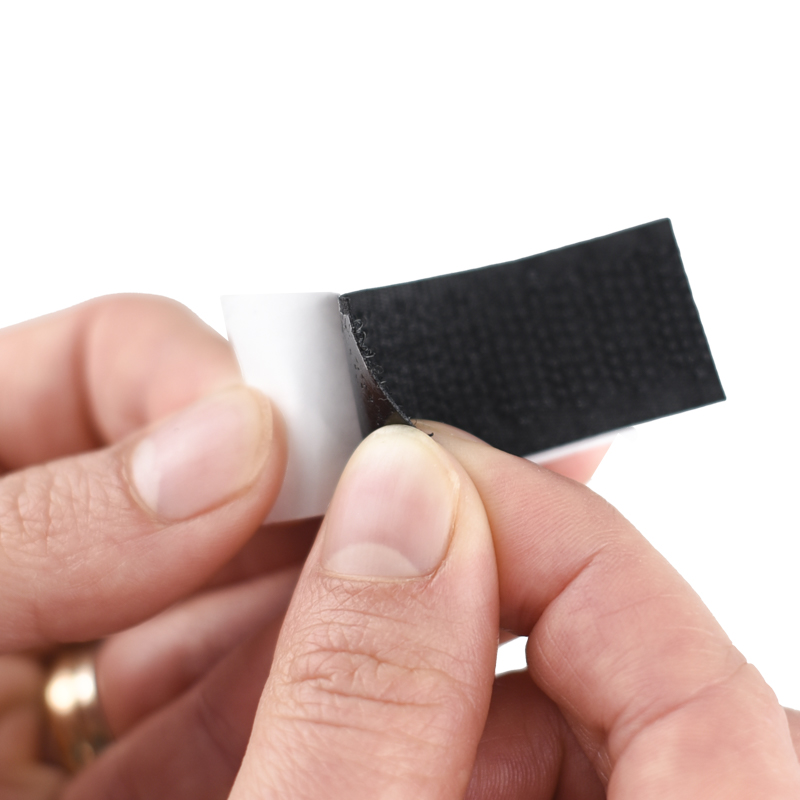
Attrezzo per zanzariera - Installazione per finestra con zanzariera Maniglia in nylon per arrotolatori a mano : Amazon.it: Commercio, Industria e Scienza